Client-Side Network Resources - AWS
The following table provides a list of resources required for client-side network configuration.
| Field | Description |
|---|---|
| Stack name | The name for this collection of AWS network resources. |
| Bation Host | Select whether you want to create a bastion host in your client-side VPC.
Important: You must create a bastion host in your client-side VPC to access private endpoints in your service.
|
| Zone Deploy | Select the number of availability zones in which you will host your client-side VPC. For highest availability, MarkLogic recommends you select three AWS availability zones per region. For details, see Supported Regions - AWS. |
| Availability Zone | Select your preferred availability zones. Select the same number of availability zones specified in the Zone Deploy field.
Important: If you use more than three availability zones, download the template and modify the file to add more entries for Private/Public Subnet CIDRs, Route Associations, and so on. Use "Upload a template to Amazon S3" as the option when creating a CloudFormation stack.
Note: For more general information on regions supported by AWS, see Regions and Availability Zones.
|
| VPC CIDR | Range of IPv4 addresses used to set up your client-side VPC. Primary CIDR (Classless Inter-Domain Routing) block for your VPC. Example: 10.0.0.0/23
Important: The CIDR range
10.128.0.0/10 is used internally. If your VPC CIDR is in the 10.128.0.0/10 range, your block size must be between a /20 netmask and /28 netmask. The maximum number of IP addresses including all subnets in this CIDR range is 4,096. |
| Public and Private Subnet CIDRs | CIDR is used to allocate an IP address for each subnet. Enter one CIDR in each field. Example: 10.0.0.0/23, 10.0.2.0/23, 10.0.4.0/23, 10.0.6.0/25, 10.0.6.128/25, 10.0.7.0/25
Important: You must provide values for all three public and private subnet CIDRs. The order is the same as the Availability Zones selected. For example, if you select one Availability Zone, the second and third public and private subnet CIDRs will be ignored.
|
| EC2 Key Name | See Creating a Key Pair.
Important: You will need the certificate file (
.pem file extension) to configure SSH tunneling. |
| Key Certificate | Private key file that is automatically downloaded by your browser after you create an EC2 key pair. For details, see Creating a Key Pair.
Important: You will need the certificate file to configure SSH tunneling.
|
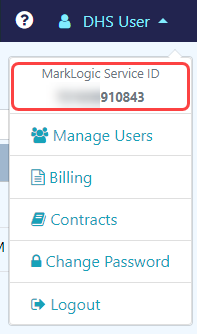
| MarkLogic Service ID | The ID that identifies you as a MarkLogic Service subscriber.
To find your MarkLogic Service ID in DHS, navigate to the MarkLogic Data Hub Service home page and click on the username in the top menu.
 |
| VPC ID | Your client-side VPC's identifier (vpc-*).
Important: The VPC ID must include the
vpc- prefix.To find your VPC ID in AWS CloudFormation Console, navigate to the AWS CloudFormation Console.
To find all of your VPC IDs in AWS, navigate to AWS.
Example: |
| Public and Private Subnet Route Table IDs | Your client-side VPC's route tables (rtb-*) used to route network subnet CIDRs to the peering connection ID (pcx-*), enabling your client-side VPC and MarkLogic VPC to communicate with each other.
To find your Route Tables in AWS CloudFormation Console if you used our template, navigate to the AWS CloudFormation Console.
To find all of your route tables in AWS, navigate to AWS.
Tip: You can filter by your VPC ID (
vpc-*) to find the route tables for your client-side VPC. |
| Service Public and Private Subnet CIDRs | The public and private subnet CIDRs calculated from the network CIDR in your peered DHS network configuration.
Enter the public subnet CIDRs in the Service Public Subnet CIDR fields and the private subnet CIDRs in the Service Private Subnet CIDR fields. Enter one CIDR in each field. Example: |
| Peering Connection ID | The Peering Connection ID (pcx-*) in your peered DHS network configuration. |